
A new report from Kaspersky reveals the top cyber threats for SMBs in 2023. Read more about it and how to protect organizations from it.
According to a new report from Kaspersky, small and medium-sized businesses are facing various cybersecurity threats; the biggest issues are exploits against their infrastructure, malware for different purposes and backdoors.
Jump to:
The biggest cybersecurity threat to SMBs is the use of exploits by attackers; there were 483,980 detections in the five first months of 2023. The successful use of exploits allows an attacker to compromise a system or a computer, elevate their privileges, plant malware, steal sensitive data or even crash systems or delete information, depending on the exploit type.
The second biggest cybersecurity threat is Trojans. Trojans are malicious software that, once installed on a system, provide the ability to install more malware or execute programs or commands in the background without alerting the users. Depending on the purpose of the Trojan, it might also be used for deleting, blocking, modifying or copying data or facilitating further compromise.
The third biggest cybersecurity threat for SMBs is backdoors, which are malware that provides remote access to attackers. Those accesses can then be used for manipulating files, exfiltrating sensitive data such as intellectual property and more.
Kaspersky’s research shows that the global number of cybersecurity attacks when comparing January 2022 to May 2022 and January 2022 to May 2023 has decreased by 42%, yet the types of attacks stayed the same (Figure A and Figure B).
Figure A
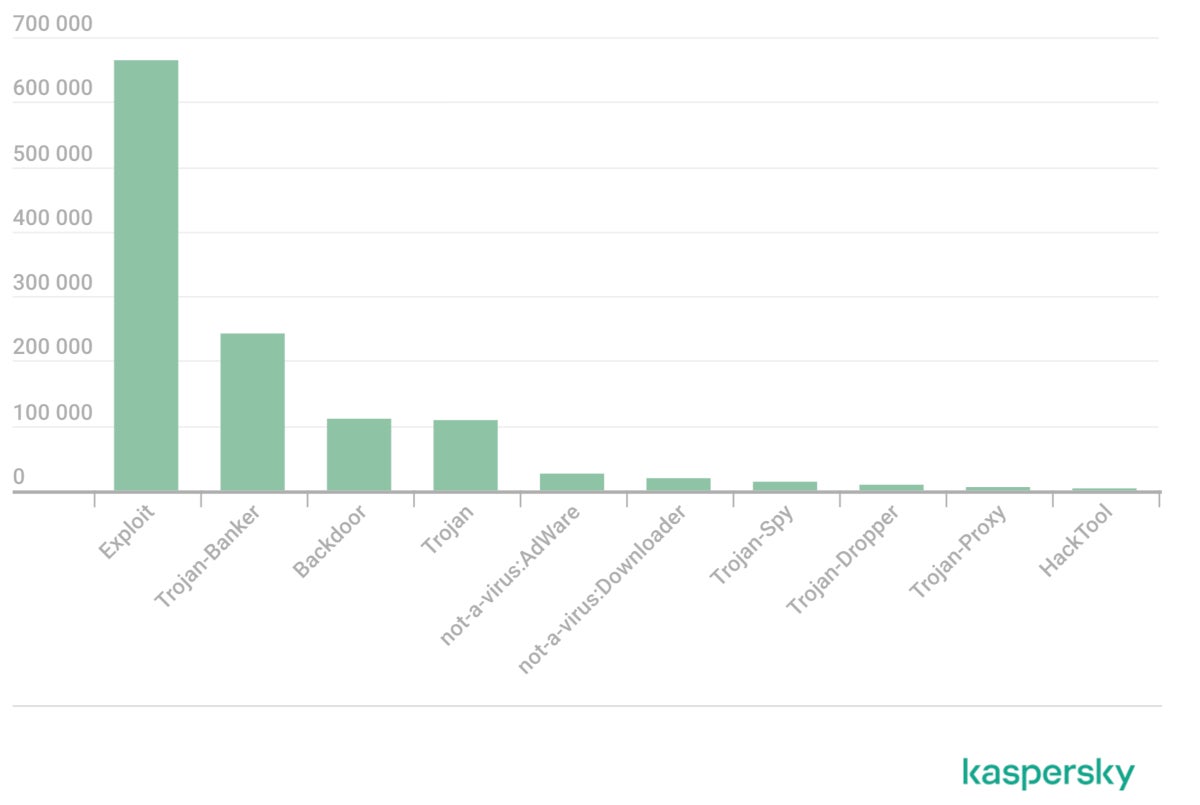
Figure B
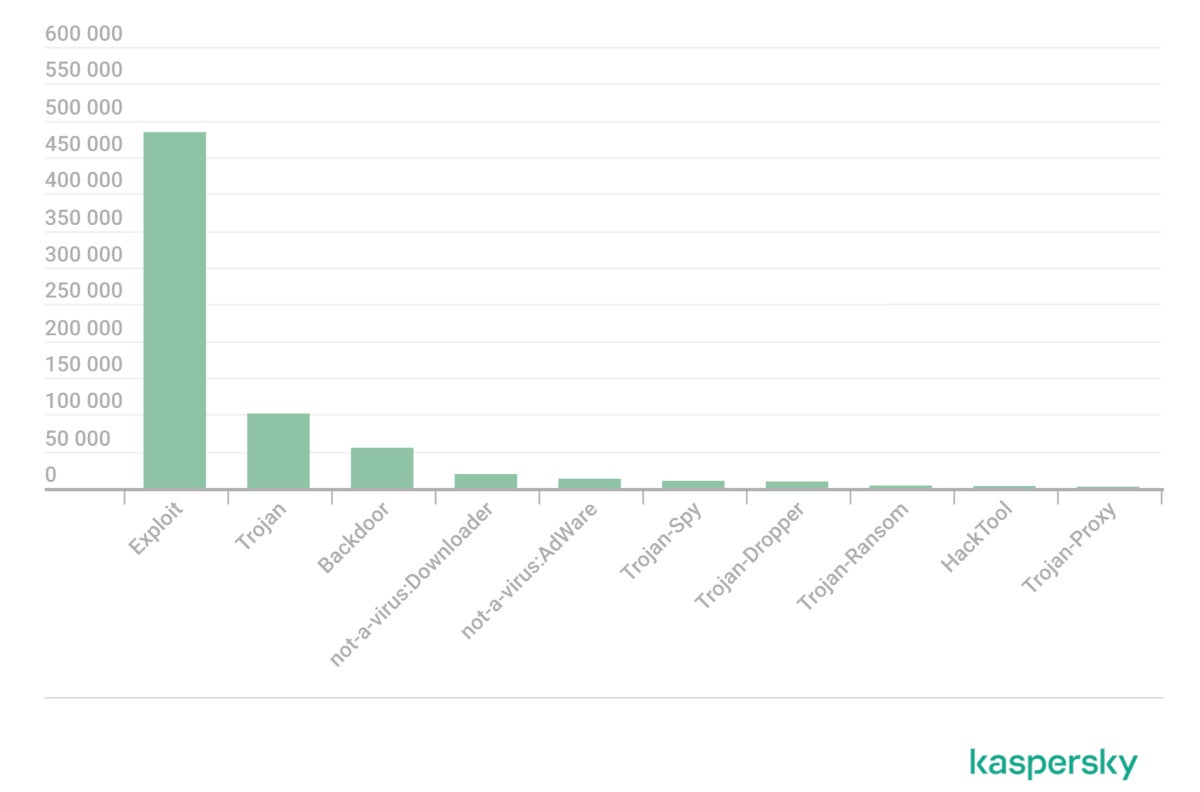
Between January 1 and May 18, 2023, a total of 1,201,436 detections were triggered, while the same period in 2022 triggered 698,423 detections.
All of these cybersecurity threats can be operated by attackers for a variety of purposes, including cyberespionage and data theft (e.g., organizations’ sensitive information, trade secrets and employees’ personally identifiable information) and financial gain operations (e.g., business email compromise operations and credit card information theft).
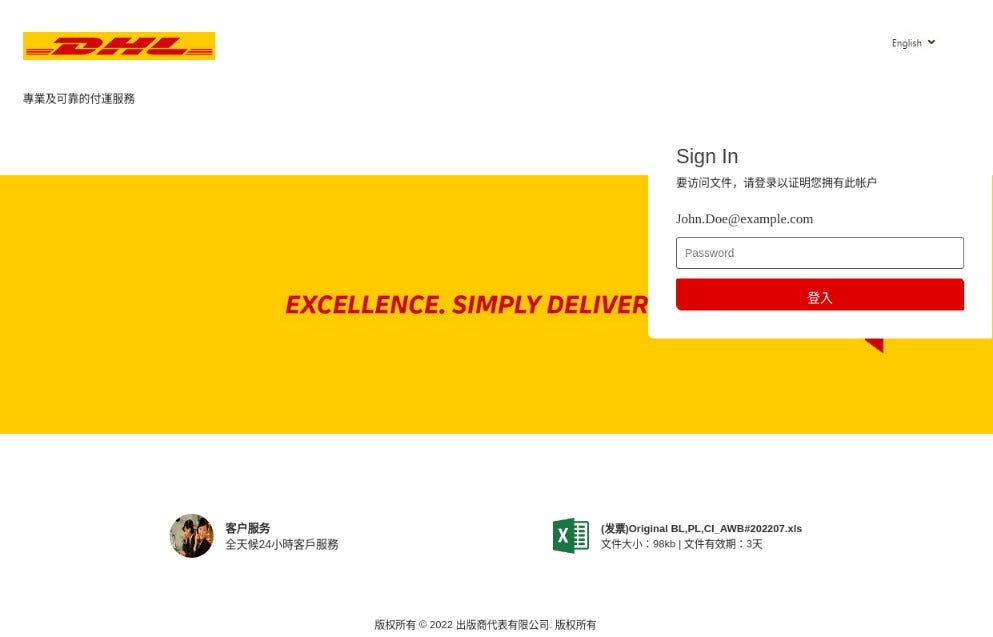
SMBs’ employees very often receive phishing emails from attackers pretending to be a legitimate service that the user operates, a trusted partner, a software vendor, a financial institution, or a delivery service (Figure C). According to research from cybersecurity leader Barracuda Networks, an average employee of an SMB receives 350% more social engineering attacks than an employee of a larger company.
Figure C
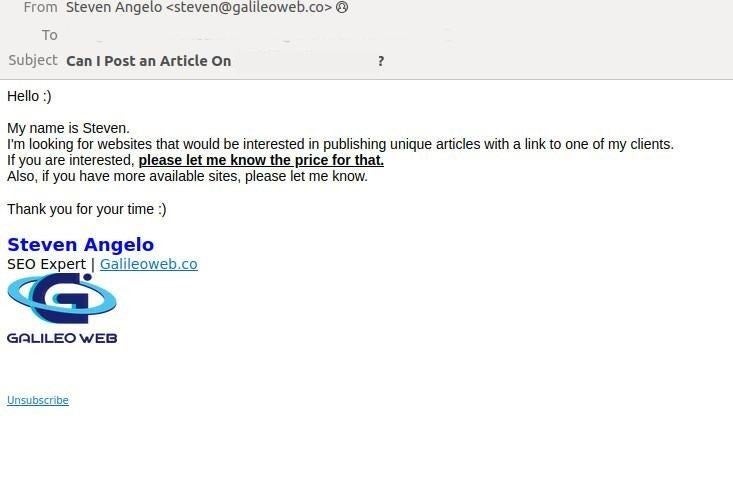
Other social engineering techniques consist of reaching users via email and offering attractive deals or money to the recipient (Figure D). Yet when the user answers, they will be tricked into providing data and possibly credentials, credit card information or corporate access, depending on the attack.
Figure D
The last example provided by Kaspersky is QBot malware diffusion. In this case, the attacker gains access to a legitimate email box of a corporate user. The emails are then selected, and the reply function is used to send a message to the original sender with a link leading to a QBot infection. The technique is known as conversation hijack as the attacker joins an existing email dialogue to try to infect more employees. Since the email answer comes from a legitimate account that has been compromised, it is very difficult to detect this cybersecurity threat.
There are various reasons why cybercriminals target SMBs, but the main two reasons are:
In the last few years, SMBs have become increasingly targeted by cybercriminals and are even more targeted than large corporations, according to Barracuda Networks.
SMBs are advised to have all systems — hardware and software — up to date and patched in order to avoid attackers using exploits against known vulnerabilities.
It is strongly recommended to use security solutions on endpoints and servers that minimize the chances of being compromised or infected by malware. Email security solutions should be deployed in order to detect and block phishing attempts. In addition, cloud storage and services should be monitored to detect any unusual activity that could be the result of an attacker’s behavior.
Access control policies should be deployed, especially for corporate VPN access, in addition to deploying multifactor authentication so an attacker cannot log in even when they are in possession of valid credentials.
Cybersecurity awareness and training programs should be provided for all employees.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.