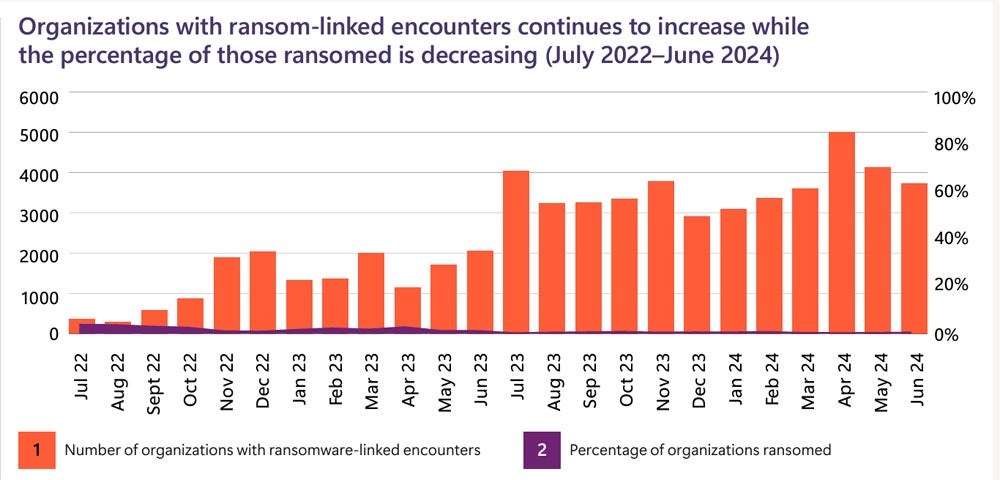
The number of attempted ransomware attacks on Microsoft customers globally have grown dramatically in the last year, according to Microsoft’s Digital Defense report, released on Oct. 15. However, advancements in automatic attack disruption technologies have led to fewer of these attacks reaching the encryption stage.
Microsoft reported 600 million cybercriminal and nation-state attacks occurring daily. While ransomware attempts increased by 2.75 times, successful attacks involving data encryption and ransom demands dropped by three-fold.
Microsoft says it “tracks more than 1,500 unique threat groups — including more than 600 nation-state threat actor groups, 300 cybercrime groups, 200 influence operations groups, and hundreds of others.” The top five ransomware families — Akira, Lockbit, Play, Blackcat, and Basta — accounted for 51% of documented attacks.
According to the report, attackers most often exploit social engineering, identity compromises, and vulnerabilities in public-facing applications or unpatched operating systems. Once inside, they often install remote monitoring tools or tamper with security products. Notably, 70% of successful attacks involved remote encryption, and 92% targeted unmanaged devices.
Other major types of attacks included:
Antivirus tampering was also a major player in the previous year: Over 176,000 incidents Microsoft Defender XDR detected in 2024 involved tampering with security settings.
SEE: Ransomware actors can target backup data to try to force a payment.
Both financially-motivated threat actors and nation-state actors increasingly use the same information stealers and command-and-control frameworks, Microsoft found. Interestingly, financially-motivated actors now launch cloud identity compromise attacks — a tactic previously associated with nation-state attackers.
“This year, state-affiliated threat actors increasingly used criminal tools and tactics — and even criminals themselves — to advance their interests, blurring the lines between nation-state backed malign activity and cybercriminal activity,” the report stated.
Microsoft tracks major threat actor groups from Russia, China, Iran, and North Korea. These nation-states may either leverage financial threat actors for profit or turn a blind eye to their activities within their borders.
According to Tom Burt, Microsoft’s corporate vice president of customer security and trust, the ransomware issue highlights the connection between nation-state activities and financially motivated cybercrime. This problem is exacerbated by countries that either exploit these operations for profit or fail to take action against cybercrime within their borders.
Expert Evan Dornbush, former NSA cybersecurity expert, offers perspectives on the matter:
“This report signals one trend currently getting little attention and likely to define the future of cyber: the amount of money criminals can earn,” he said in an email to TechRepublic. “Per the Microsoft report, government, as a sector, only makes up 12% of the aggressors’ targeting sets. The vast majority of victims are in the private sector.”
The sectors most targeted by nation-state threat actors this year were:
Generative AI introduces a new set of questions. Microsoft recommends limiting generative AI’s access to sensitive data and ensuring that data governance policies are applied to its use. The report outlines AI’s significant impacts on cybersecurity:
“The sheer volume of attacks must be reduced through effective deterrence,” Burt explained, “and while the industry must do more to deny the efforts of attackers via better cybersecurity, this needs to be paired with government action to impose consequences that further discourage the most harmful cyberattacks.”
The Microsoft report contains actions organizations can take to prevent specific types of attacks. TechRepublic distilled some actionable insights that apply across the board:
Microsoft put its Secure Future Initiative in place this year, after the Chinese intrusion into Microsoft government email accounts in July 2023.