New research from cybersecurity company Volexity revealed details about a highly sophisticated attack deployed by a Chinese-speaking cyberespionage threat actor named StormBamboo.
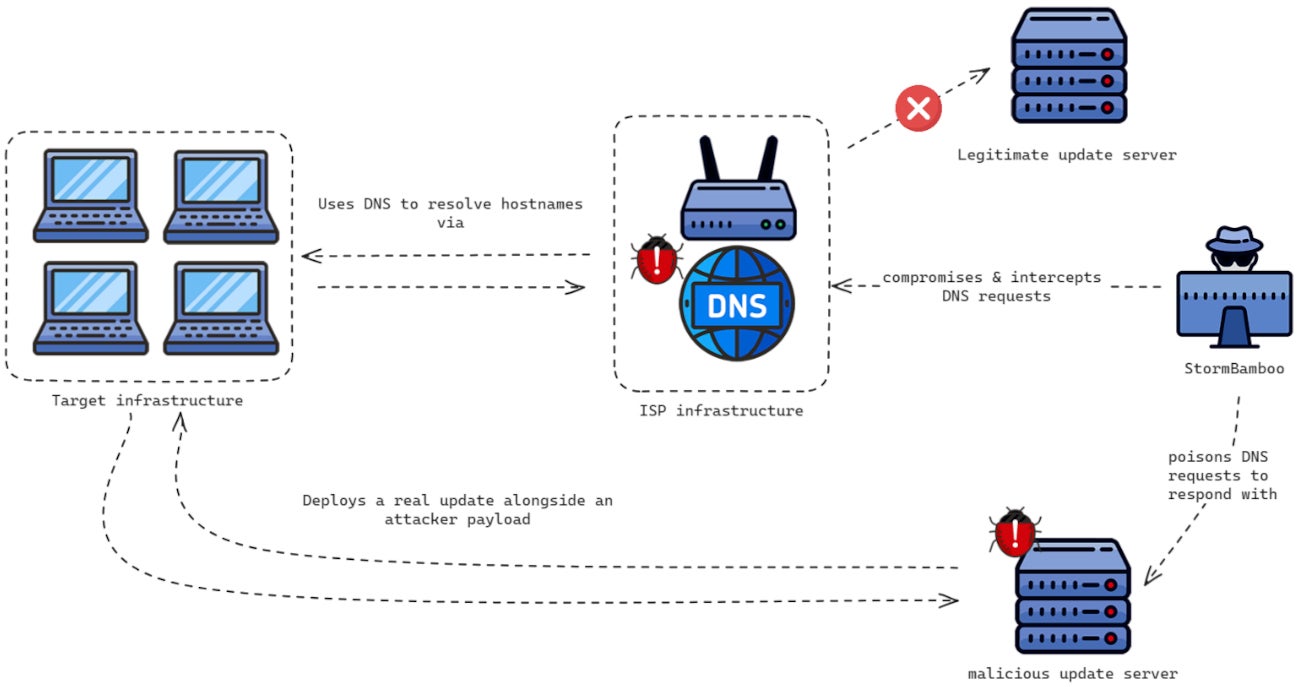
StormBamboo compromised an ISP to modify some DNS answers to queries from systems requesting legitimate software updates. Multiple software vendors were targeted. The altered responses led to malicious payloads served by StormBamboo in addition to the legitimate update files. The payloads targeted both macOS and Microsoft Windows operating systems.
StormBamboo — also known as Evasive Panda, Daggerfly, or Bronze Highland — is a China-aligned cyberespionage threat actor, active since at least 2012. The Chinese-speaking group has targeted many organizations that align with Chinese interests worldwide.
Over the years, the group has targeted individuals in mainland China, Hong Kong, Macao, and Nigeria. Additionally, it has targeted entities, including governments, in Southeast Asia, East Asia, the U.S., India, and Australia.
The group has a long history of compromising legitimate infrastructures to infect their targets with custom malware developed for Microsoft Windows and macOS operating systems. The group has deployed watering hole attacks, consisting of compromising a specific website to target its visitors and infect them with malware.
StormBamboo is also capable of running supply chain attacks, such as compromising a software platform, to discreetly infect people with malware.
The group is also capable of targeting Android users.
The threat actor managed to compromise a target’s ISP infrastructure to control the DNS responses from that ISP’s DNS servers.
DNS servers mostly consist of translating domain names to IP addresses, leading them to the correct website. An attacker controlling the server can cause the computers to request a particular domain name to an attacker-controlled IP address. This is exactly what StormBamboo did.
While it is not known how the group compromised the ISP, Volexity reported the ISP rebooted and took various components of its network offline, which immediately stopped the DNS poisoning operation.
The attacker aimed at altering DNS answers for several different legitimate application update websites.
SEE: Why your company should consider implementing DNS security extensions
Paul Rascagneres, threat researcher at Volexity and an author of the publication, told TechRepublic in a written interview the company doesn’t exactly know how the threat actors chose the ISP.
“The attackers probably did some research or reconnaissance to identify what is the victim’s ISP,” he wrote. “We don’t know if other ISPs have been compromised; it is complicated to identify it from the outside. StormBamboo is an aggressive threat actor. If this operating mode was a success for them, they could use it on other ISPs for other targets.”
Multiple software vendors have been targeted by this attack.
Once a DNS request from users was sent to the compromised DNS server, it answered with an attacker-controlled IP address that delivered a real update for the software — yet with an attacker’s payload.
The Volexity report showed that multiple software vendors using insecure update workflows were concerned and provided an example with a software named 5KPlayer.
The software checks for updates for “YoutubeDL” every time it is started. The check is done by requesting a configuration file, which indicates if a new version is available. If so, it is downloaded from a specific URL and executed by the legitimate application.
Yet the compromised ISP’s DNS will lead the application to a modified configuration file, which indicates there is an update, but delivers a backdoored YoutubeDL package.
The malicious payload is a PNG file containing either MACMA or POCOSTICK/MGBot malware, depending on the operating system requesting the update. MACMA infects MacOS, while POCOSTICK/MGBot infects Microsoft Windows operating systems.
POCOSTICK, also known as MGBot, is a custom malware possibly developed by StormBamboo, as it has not been used by any other group, according to ESET. The malware has existed since 2012 and consists of several modules enabling keylogging, file stealing, clipboard interception, audio streams capture, cookie, and credential theft.
Conversely, MACMA allows keylogging, victim device fingerprinting, and screen and audio capture. It also provides a command line to the attacker and has file-theft capabilities. Google initially reported in 2021 the presence of MACMA malware, using watering hole attacks to be deployed.
The Google attack was not attributed to a threat actor, yet it targeted visitors of Hong Kong websites for a media outlet and a prominent pro-democracy labor and political group, according to Google. This attack aligns with StormBamboo’s targeting.
Volexity also noticed significant code similarities between the latest MACMA version and another malware family, GIMMICK, used by the StormCloud threat actor.
Finally, in one case following a victim’s macOS device compromise, Volexity saw the attacker deploy a malicious Google Chrome extension. The obfuscated code allows the attacker to exfiltrate the browser’s cookies to an attacker-controlled Google Drive account.
Rascagneres told TechRepublic that Volexity identified several targeted insecure update mechanisms from different software: 5k Player, Quick Heal, Sogou, Rainmeter, Partition Wizard, and Corel.
Questioned about how to protect and improve the update mechanisms at the software vendor level, the researcher insists that “the software editors should enforce HTTPS update mechanism and check the SSL certificate of the website where the updates are downloaded. Additionally, they should sign the updates and check this signature before executing them.”
In order to help companies detect StormBamboo activity on their systems, Volexity provides YARA rules to detect the different payloads and recommends blocking the Indicators of Compromise the company provides.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.