Many macOS and iOS applications were open to a vulnerability in CocoaPods, an open-source dependency manager, E.V.A. Information Security revealed on July 1. The vulnerability has been patched since EVA first discovered it, and no attacks have occurred that are conclusively related to it.
However, the case is interesting because the vulnerability stayed unnoticed for so long and highlighted how developers should be careful with open-source libraries. The vulnerability is a good reminder for developers and DevOps teams to check whether any of their organizations’ devices might be affected.
“Thousands of applications and millions of devices” could have been impacted downstream, E.V.A. said. The security team says they found vulnerable CocoaPods pods in “the documentation or terms of service documents of applications provided by Meta (Facebook, Whatsapp), Apple (Safari, AppleTV, Xcode), and Microsoft (Teams); as well as in TikTok, Snapchat, Amazon, LinkedIn, Netflix, Okta, Yahoo, Zynga, and many more.”
E.V.A. reported the vulnerability to CocoaPods in October 2023, at which point it was patched.
“The CocoaPods team responded responsibly and swiftly to the vulnerabilities once disclosed,” E.V.A. Information Security wrote.
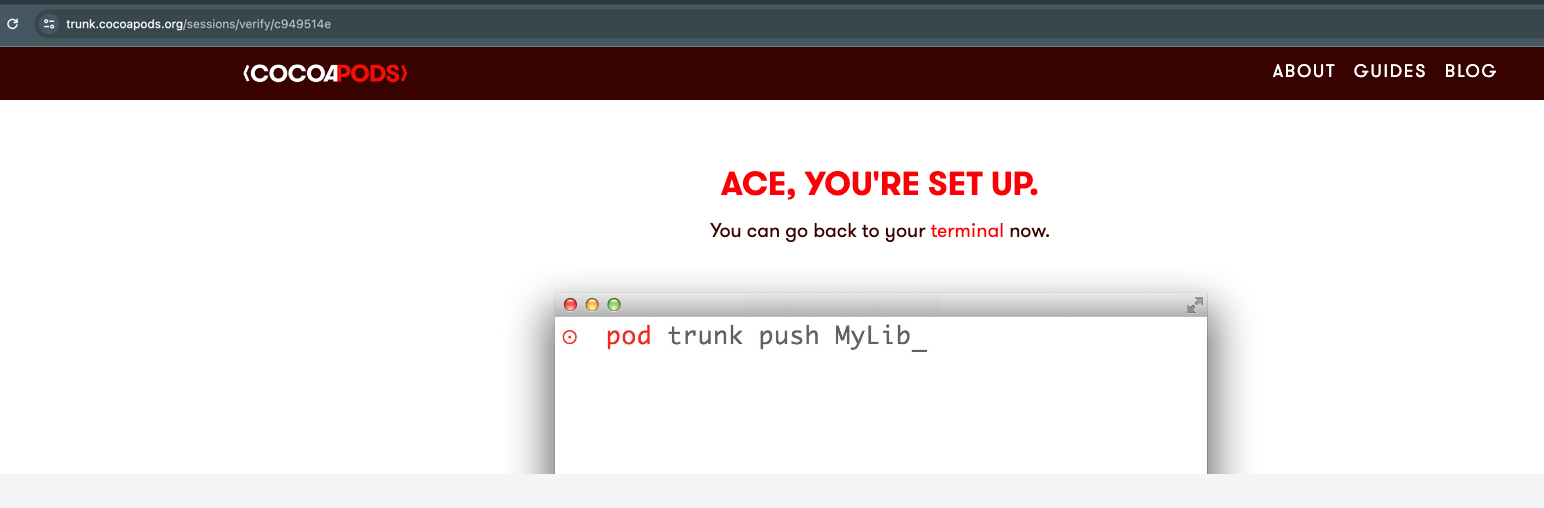
CocoaPods is a dependency manager for Swift and Objective-C projects, and it verifies the legitimacy of open-source components. E.V.A. Information Security wasn’t originally hunting for vulnerabilities in CocoaPods; instead, the team discovered them when red teaming for a customer.
SEE: CISA recommends using memory-safe programming languages for open-source projects.
E.V.A. reported several causes for the vulnerabilities. First, CocoaPods migrated from GitHub to a “trunk” server in 2014, but the pod owners needed to manually reclaim their spots. Some of them didn’t, leaving 1,866 “orphaned” pods that sat untouched for the next 10 years. Anyone could email CocoaPods to claim those pods, which would have allowed attackers to inject malicious content.
Second, attackers could run malicious code on the “trunk” server itself by exploiting an insecure email verification workflow. From there, they could manipulate or replace packages downloaded from that server.
Third, attackers could steal account verification tokens by spoofing an HTTP header and taking advantage of misconfigured email security tools. From there, they could use that token to change packages on the CocoaPods server, which could potentially lead to supply chain and zero-day attacks.
The CocoaPods vulnerabilities are a good reminder to developers and DevOps teams not to forget about dependency managers, which could be a potential weak link in supply chain security. To handle the CocoaPods vulnerabilities, developers and DevOps teams should double check the open-source dependencies used in their application code.
E.V.A. suggested: