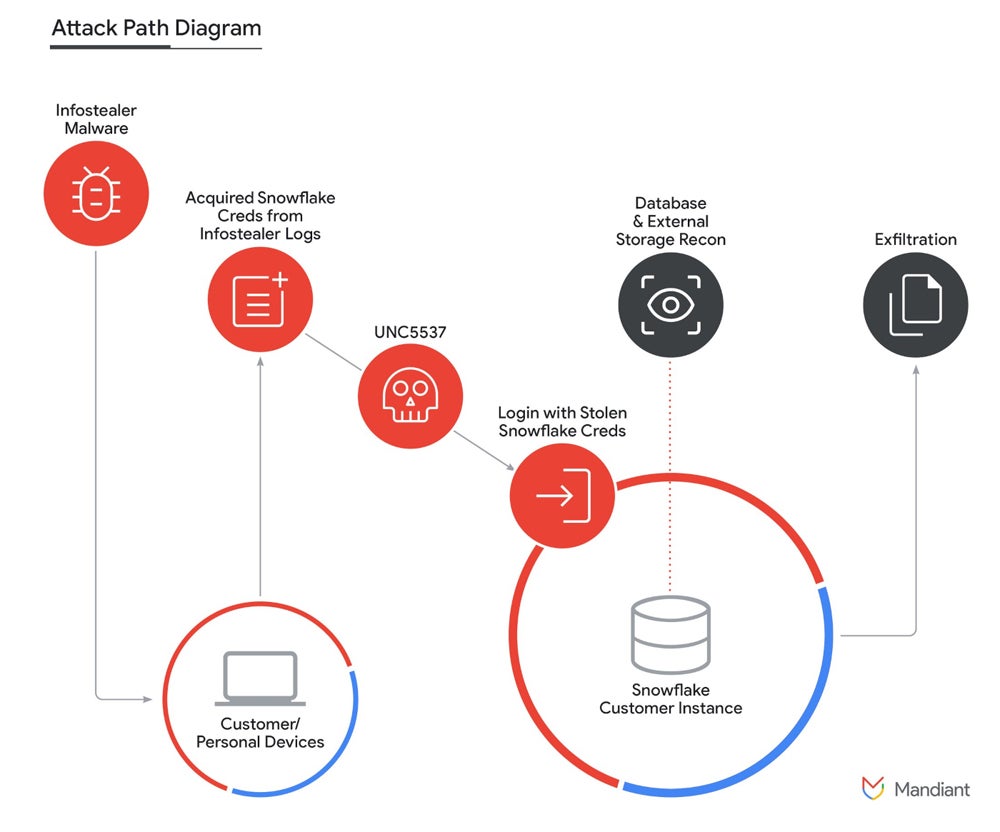
A new report from Mandiant, part of Google Cloud, reveals that a financially motivated threat actor named UNC5537 collected and exfiltrated data from about 165 organizations’ Snowflake customer instances. Snowflake is a cloud data platform used for storing and analyzing large volumes of data.
The threat actor managed to get access to these data by triggering credentials that were previously stolen by infostealer malware or purchased from other cybercriminals.
According to Mandiant, the threat actor UNC5537 advertises victim data for sale on cybercrime forums and attempts to extort many of the victims. When the data is sold, any cybercriminal might buy this information for different purposes such as cyber espionage, competitive intelligence or more financially-oriented fraud.
A joint statement provided by Snowflake, Mandiant and cybersecurity company CrowdStrike indicates there is no evidence suggesting the fraudulent activity would be caused by a vulnerability, misconfiguration or breach of Snowflake’s platform. There is also no evidence the activity would have been caused by compromised credentials from current or past Snowflake employees.
Instead, evidence shows the attackers obtained credentials from multiple infostealer malware campaigns that infected non-Snowflake owned systems. The threat actor then gained access to the affected accounts, which allowed the exfiltration of a significant volume of customer data from the respective Snowflake customer instances.
Mandiant researchers stated the majority of the credentials used by UNC5537 were available from historical infostealer malware; some of those credentials date back to November 2020 but were still usable. Different infostealer malware families were responsible for the credentials theft — the most used ones being Vidar, Risepro, Redline, Racoon Stealer, Lumma and Metastealer.
According to Mandiant and Snowflake, at least 79.7% of the accounts leveraged by the threat actor had prior credential exposure.
Mandiant also reported the initial compromise of infostealer malware occurred on contractor systems that were also used for personal activities, including gaming and downloads of pirated software, which is a strong vector for spreading infostealers.
As reported, the threat actor obtained credentials from a variety of infostealer malware, yet UNC5537 also leveraged credentials that were previously purchased.
While no additional information is provided by Mandiant, it is reasonable to think those credentials were bought in one or several cybercriminal underground marketplaces directly to so-called Initial Access Brokers, which are a category of cybercriminals who sell stolen corporate access to other fraudsters.
As written by Mandiant in its report, “the underground infostealer economy is also extremely robust, and large lists of stolen credentials exist both for free and for purchase inside and outside of the dark web.” Mandiant also reported that, in 2023, 10% of overall intrusions began with stolen credentials, representing the fourth most notable initial intrusion vector.
In this attack campaign, the initial access to Snowflake customer instances often occurred via the native user interface accessible from the web (Snowflake SnowSight) or from the command-line interface tool provided by Snowflake (SnowSQL). An additional attacker-named tool called “rapeflake” and tracked under FROSTBITE by Mandiant has been used to perform reconnaissance against Snowflake instances.
FROSTBITE exists in at least two versions: one using .NET to interact with the Snowflake .NET driver, and one version using Java to interact with the Snowflake JDBC driver. The tool allows the attackers to perform SQL activities such as listing users, current roles, current IP addresses, session IDs and organizations’ names.
A public tool for managing databases, DBeaver Ultimate, has also been used by the threat actor to run queries on the Snowflake instances.
Using SQL queries, the threat actor was able to exfiltrate information from databases. Once interesting data was found, it was compressed as GZIP using the “COPY INTO” command to reduce the size of the data to be exfiltrated.
The attacker primarily used Mullvad and Private Internet Access VPN services to access the victims’ Snowflake instances. A moldovan VPS provider, ALEXHOST SRL, was also used for data exfiltration. The threat actor stored victim data on several international VPS providers, as well as on the cloud storage provider MEGA.
The attack campaign appears to be a targeted campaign aimed at Snowflake users with single-factor authentication. All users with multifactor authentication are safe from this attack campaign and were not targeted.
In addition, the impacted Snowflake customer instances did not have allow lists in place to only allow connections from trusted locations.
Snowflake published information on detecting and preventing unauthorized user access.
The company provided a list of almost 300 suspicious IP addresses used by the threat actor and shared a query to identify access from the suspect IP addresses. The company also provided a query to identify the usage of the “rapeflake” and “DBeaver Ultimate” tools. Any user account returning results from those queries must immediately be disabled.
Security hardening is highly recommended by Snowflake:
Additionally, it is strongly recommended to have all software and operating systems up to date and patched to avoid being compromised by a common vulnerability, which might lead to credentials leak.
Security solutions need to be deployed on every endpoint to prevent infostealer infection.
It is also advised to raise awareness on computer security and train staff to detect and report suspicious cybersecurity events.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.