A new strain of ransomware dubbed ShrinkLocker is being used by cyberattackers to target enterprise computers. It exploits the Microsoft BitLocker encryption feature to encrypt the entire local drive and remove the recovery options before shutting down the PC. ShrinkLocker was discovered by cybersecurity firm Kaspersky, and analysts have observed variants in Mexico, Indonesia and Jordan.
BitLocker has been used to stage ransomware attacks in the past, but this strain has “previously unreported features to maximise the damage of the attack,” Kaspersky said in a press release. ShrinkLocker is unique in that it can check the version of a device’s Windows operating system to ensure it enables the appropriate BitLocker features, but deletes itself if it can’t.
Cristian Souza, incident response specialist at Kaspersky Global Emergency Response Team, said in the press release, “What is particularly concerning about this case is that BitLocker, originally designed to mitigate the risks of data theft or exposure, has been repurposed by adversaries for malicious ends. It’s a cruel irony that a security measure has been weaponized in this way.”
Companies in steel and vaccine manufacturing, as well as a government entity, have been targeted with ShrinkLocker so far. However, Souza told TechRepublic there “is no evidence to believe that this group is targeting specific industries,” as victims are from different countries and sectors.
BitLocker is currently only available on the Pro, Enterprise, Education and Ultimate editions of Windows operating systems, but it will be included and automatically activated in all versions with the release of Windows 11 24H2 later this year. This significantly increases the potential scope of ShrinkLocker victims.
“Infections by ShrinkLocker can be critical if the victim does not have adequate proactive and reactive measures in place,” Souza added. “Since BitLocker is a native Windows feature, any machine with Windows Vista+ or Server 2008+ could be affected.”
Although ShrinkLocker self-deletes after encrypting the target, Kaspersky analysts were able to discover how it works by studying a script left behind on a drive on a PC that was infected but did not have BitLocker configured.
Attackers might deploy ShrinkLocker on a device by exploiting unpatched vulnerabilities, stolen credentials or internet-facing services to gain access to servers. A user may also unintentionally download the script, for example, through a link in a phishing email.
“Once they have access to the target system, the attacker can try to exfiltrate information and finally execute the ransomware to encrypt the data,” Souza told TechRepublic.
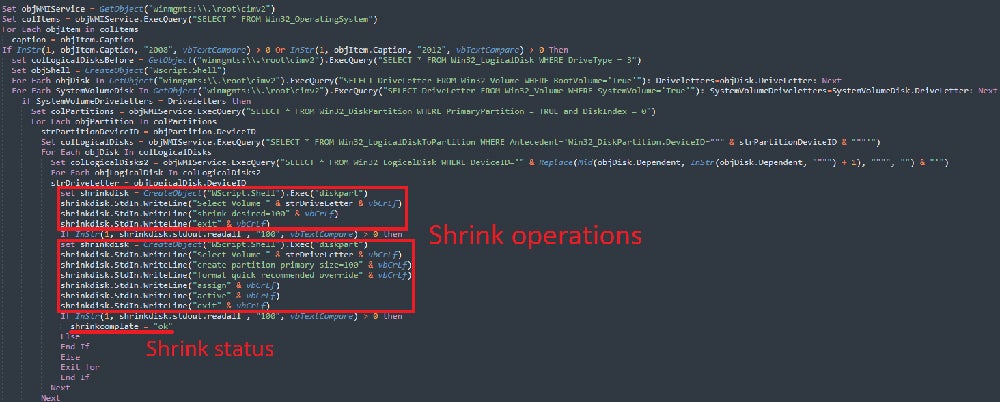
Once the script is triggered, it uses Windows Management Instrumentation extensions and the Win32_OperatingSystem class to query information about the device’s operating system and domain. If the device runs on Windows XP, 2000, 2003 or Vista, or the current domain of the queried objects does not match the target, the script deletes itself.
SEE: Is there a simple way to recover encrypted BitLocker drives?
However, if the PC is using Windows 2008 or earlier, the script will move on to resizing its local fixed drives. It shrinks non-boot partitions by 100MB to create unallocated disk space, which is why it has been dubbed ShrinkLocker. New primary partitions are created in the unallocated space, and the boot files are reinstalled so the system can be rebooted with the encrypted files by the victim.
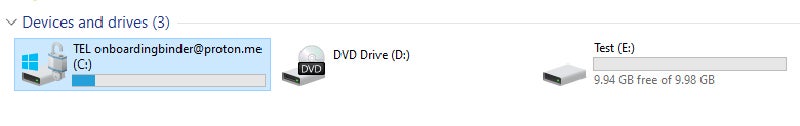
Next, the script modifies Windows registry entries to disable Remote Desktop Protocol connections and enforce BitLocker settings like PIN requirements. It then renames the boot partitions with the attacker’s email — onboardingbinder[at]proton[dot]me or conspiracyid9[at]protonmail[dot]com — and replaces existing BitLocker key protectors to prevent recovery.
ShrinkLocker creates a new 64-character encryption key using the random multiplication and replacement of the following elements:
It then enables BitLocker encryption on all of the device’s drives. ShrinkLocker only encrypts the local, fixed drive of the infected PC and does not infect network drives likely to help evade detection.
The 64-character key and some system information are sent to the attacker’s server via an HTTP POST request to a randomly generated subdomain of ‘trycloudflare[dot]com.’ This is a legitimate domain from CloudFlare that is intended to be used by developers for testing out CloudFlare Tunnel without adding a site to CloudFlare’s DNS. The attackers exploit it here to hide their real address.
Finally, ShrinkLocker self-deletes its script and scheduled tasks, clears the logs, turns on the firewall and deletes all the rules before forcing a shutdown. When the user reboots the device, they are presented with the BitLocker recovery screen with no recovery options available — all the PC’s data is encrypted, locked and out of reach.
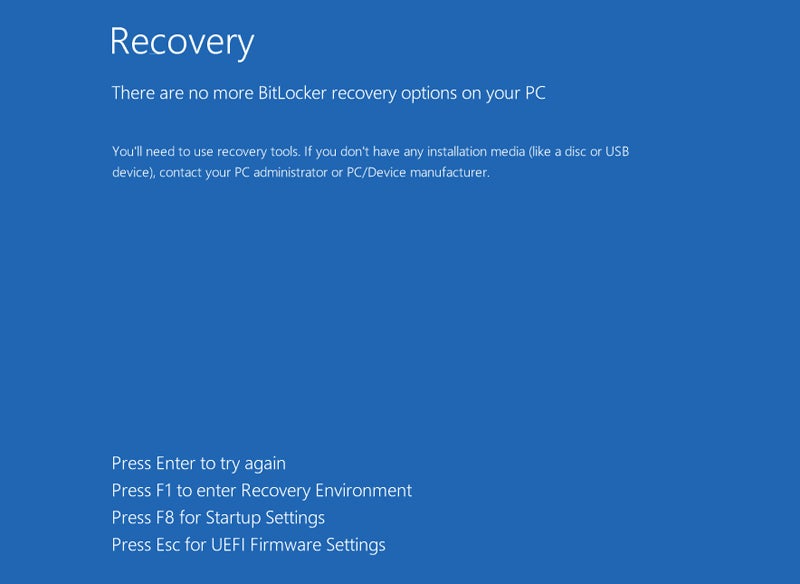
The new drive labels with the attacker’s email instruct the user to contact them, implying a ransom demand for the decryption key.
In a technical analysis, Kaspersky analysts describe both the detection of a ShrinkLocker attack and the decryption process as “difficult.” The latter is particularly hard because the malicious script contains variables that are different for each affected system.
Kaspersky experts have, so far, not been able to identify the source of the ShrinkLocker attacks or where the decryption keys and other device information are sent. However, some information about the attackers can be gleaned from the malware script.
The analysts said that the script, written in VBScript, “demonstrates that the malicious actor(s) involved in this attack have an excellent understanding of Windows internals.”
The labels containing the attacker’s email address can only be viewed if the infected device is booted by an admin in a recovery environment or with diagnostic tools, according to BleepingComputer. Furthermore, the BitLocker recovery screen can have a custom note added, yet the attackers specifically chose not to create one.
The fact that the attackers appear to have intentionally made it difficult to contact them suggests their motives are disruption and destruction rather than financial gain.
“For now, we know we are dealing with a very skilled group,” Souza told TechRepublic. “The malware we were able to analyse shows that the attackers have a deep understanding of the operating system’s internals and various living-off-the-land tools.”
Kaspersky provides the following advice to businesses looking to protect their devices from the ShrinkLocker infection:
BitLocker has been targeted by bad actors numerous times in the past, well before the emergence of ShrinkLocker. In 2021, a hospital in Belgium had 40 servers and 100 TB of its data encrypted after an attacker exploited BitLocker, leading to delays in surgeries and the redirection of patients to other facilities.
The following year, another attacker targeted one of Russia’s largest meat suppliers in the same way, before Microsoft reported the Iranian government had sponsored a number of BitLocker-based ransomware attacks that demanded thousands of U.S. dollars for the decryption key.