Highlights from CrowdStrike’s 2024 report:
CrowdStrike’s new 2024 Global Threat report exposed the latest trends in cyberattacks, and we’re highlighting the main topics of interest for enterprises.
The cyberattacks ecosystem keeps growing, with CrowdStrike observing 34 new threat actors in 2023. Attackers increasingly target cloud environments, mostly for financial motives. Yet in some cases, it allows attackers to reach on-premise servers.
Supply chain attacks are often used, as those attacks allow a threat actor to hit multiple targets easily. Organizations operating in the tech sector are also uniquely at risk from those attacks, as nearly every trusted-relationship compromise originated from intrusions into organizations providing commercial software. End of Life products and unmanaged devices in the network periphery are also targeted.
While phishing is still a valid method to obtain credentials from employees of targeted organizations, other authentication data is also used to conduct attacks. No matter the motivation for a cybersecurity attack, identity-based and social engineering attacks are still taking center stage.
For example, the FANCY BEAR threat actor conducted phishing campaigns in 2023 and developed a custom toolkit to collect credentials from Yahoo! Mail and ukr.net webmail users. The toolkit made use of the Browser-in-the-Browser technique and added multifactor authentication interception capabilities to collect one-time passwords used in the authentication.
SCATTERED SPIDER used SMS phishing (smishing) and voice phishing (vishing) to get credentials. And the threat actor leveraged earlier intrusions at telecom organizations to run SIM swap operations on targeted employees; once the SIM swap is active, the threat actor could receive SMS messages with OTP codes directly. Additionally, the threat actor often used residential proxies to bypass detections based on the physical location of their target.
API keys and secrets are also targeted by attackers — owning those allows a cybercriminal to maintain indefinite access as long as the API keys or secrets are not changed. Cookie session and token theft were also used in 2023 by threat actors.
In addition, attackers steal or forge Kerberos tickets to gain access to encrypted credentials that can be cracked offline. A huge 583% increase in Kerberoasting attacks has been observed by CrowdStrike.
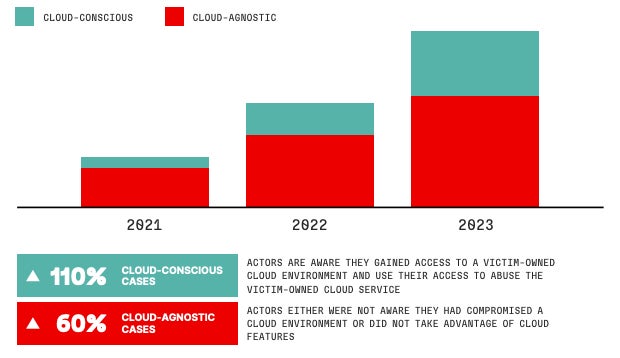
CrowdStrike noted that cloud-environment intrusions have increased globally by 75% from 2022 to 2023 (Figure A).
In CrowdStrike’s analysis, the team separates cloud-conscious cases (i.e., cases in which the attacker is aware of the cloud environment and makes use of it) and cloud-agnostic cases (i.e., an attacker does not notice the cloud environment or does not use it).
Cloud-conscious cases have increased by 110%, while cloud-agnostic cases have increased by 60% from 2022 to 2023.
Cybercriminals with financial motivation are the most active in targeting cloud environments; they are responsible for 84% of all cloud-conscious intrusions, while targeted intrusions only represent 16%.
Attackers might leverage cloud-environment intrusions to target corporate networks. As an example, the SCATTERED SPIDER threat actor often uses the victim’s Microsoft 365 environments to search for VPN instructions before using the VPN to access and move laterally inside the internal network of the targeted organization.
Targeted intrusion actors consistently attempted to exploit trusted relationships to gain access to organizations across multiple verticals and regions in 2023, according to CrowdStrike’s report.
Those attacks have an interesting return on investment for attackers: compromising a third-party that provides IT services or a third-party that is part of a software supply chain can lead to hundreds or thousands of follow-on targets. Those attacks can also more effectively help attackers targeting a hardened organization.
For example, JACKPOT PANDA used a trojanized installer for CloudChat, a China-based popular chat application often used by gambling communities, which in the end infected users with a malware named XShade.
In another case, an unidentified threat actor compromised an India-based information security software vendor to distribute malware via the legitimate software update process.
According to CrowdStrike, trusted-relationship compromises will continue to attract targeted intrusion actors in the immediate future. Organizations operating in the technology sector are at higher risk because they provide their services to a lot of organizations worldwide.
Over the course of 2023, CrowdStrike added 34 new threat actors — which they also call adversaries — to its list of 232 actors. In addition to these known adversaries, CrowdStrike tracks more than 130 active and malicious activity clusters.
Dedicated Data Leak sites showed a 76% increase over 2022 in the number of victims being exposed, which brings the total victim count to 4,615 for 2023. Newly emerged Big Game Hunting players are one of the factors that increased the number of victims, in addition to the growth of existing adversary operations and high-volume campaigns such as multiple Graceful Spider threat actor operations. This threat actor exploited three zero-day vulnerabilities to collect data from hundreds of victims worldwide.
Gaining an initial foothold on a targeted network is generally only the first phase of an attack; once they’re in, the attackers need to break out of the first compromised device and move laterally to other parts of the network to reach their goals.
The average breakout time for interactive eCrime intrusion activity dropped from 84 minutes to 62 minutes between 2022 and 2023, with the fastest breakout time being 2 minutes and 7 seconds.
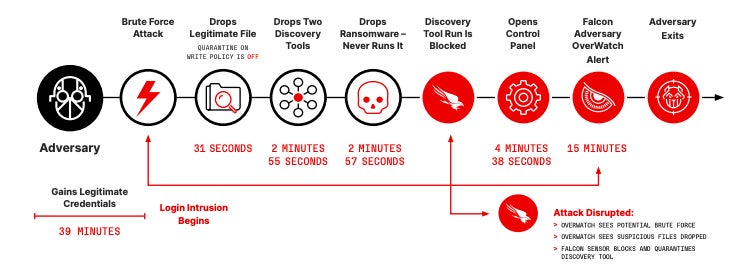
In an example provided by CrowdStrike, an attacker dropped legitimate tooling 31 seconds after the login intrusion started to run a reconnaissance operation on the network and obtain system information. Then, the attacker dropped additional files, with more tools being added within 3 minutes, including ransomware (Figure B).
According to the report, attackers also gain time by using less malware and more effective means, such as using stolen credentials and exploiting trusted relationships vulnerabilities. Malware-free activities now represent 75% of all detections in 2023, as compared to 71% in 2022 and less than 62% before 2021. The success of identity attacks and the purchase of valid credentials from initial access brokers explain this trend of using less malware.
Due to the increased use of endpoint detection and response sensors, threat actors have adapted their exploitation tactics for initial access and lateral movements by targeting the network periphery (Figure C).
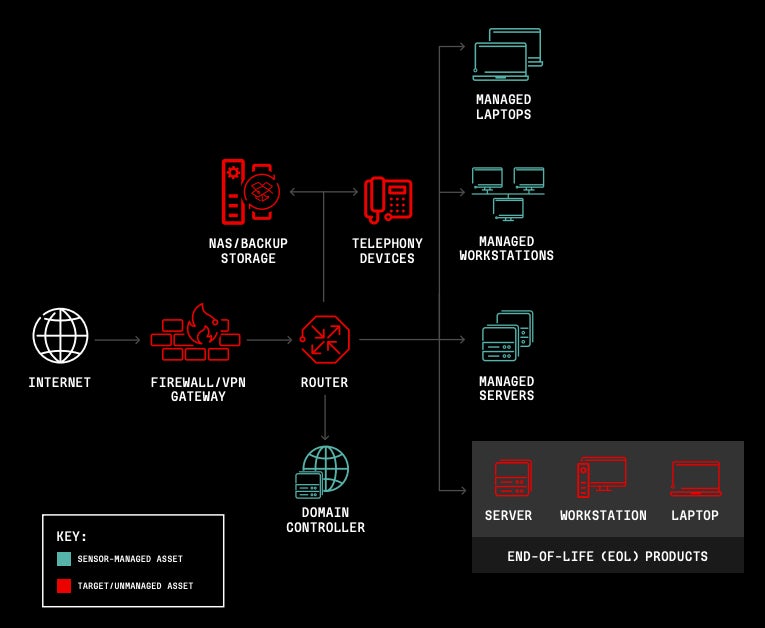
Some devices are not necessarily monitored by security solutions inside a corporate network. In particular, edge gateway devices are often based on obsolete architecture and therefore vulnerable to several vulnerabilities that might be exploited by attackers.
Vulnerabilities in firewalls and VPN platforms have, for example, hit Cisco, Citrix and F5 in 2023. Routers, mobile phones or NAS/backup storage might also be hit.
CrowdStrike highlighted another trend observed in 2023: The attacker’s focus on End of Life product exploitation. Those products, which are not patched anymore and often do not allow modern security solutions deployment, are targeted by attackers who actively develop exploits to abuse those products.
SEE: Botnet Attack Targeted Routers: A Wake-Up Call for Securing Remote Employees’ Hardware
According to CrowdStrike, it is essential to implement phishing-resistant MFA and extend it to legacy and protocols, in addition to educating teams on social engineering.
User awareness programs should be initiated to understand and fight phishing and social engineering techniques.
Technology that can detect and correlate threats across identity, endpoint and cloud environments must be implemented.
Cloud Native Application Protection Platforms that include pre-runtime protection, runtime protection and agentless technology should be favored to isolated cloud security tools that do not provide a unified platform for monitoring and detecting potential threats and vulnerabilities.
Since attackers tend to use less malware and use valid credentials and legitimate tools, it is difficult for defenders to differentiate between normal user and attacker activity; an understanding of the relationships between identity, cloud, endpoint and data protection telemetry is mandatory for that task. A consolidated security platform providing complete visibility in one place must be implemented.
In addition, defenders should prioritize patching exposed products and getting rid of EOL products.
Disclosure: I work for Trend Micro, but the views expressed in this article are mine.