Apple sent a threat notification to iPhone users in 92 countries on April 10 informing them that their device was “being targeted by a mercenary spyware attack.” The alert, sent at 12:00 p.m. Pacific Time, told recipients that the attackers were attempting to “remotely compromise” their phone and that they were likely being targeted specifically “because of who you are or what you do.” Apple’s notification did not identify the alleged attackers, nor did it specify the locations of its recipients.
iPhone users who have received the mercenary spyware attack alert should enlist expert cybersecurity help, Apple stated on its dedicated support page.
The emailed message has been seen by TechCrunch and Reuters. It reportedly reads:
“Apple detected that you are being targeted by a mercenary spyware attack that is trying to remotely compromise the iPhone associated with your Apple ID -xxx-,
“This attack is likely targeting you specifically because of who you are or what you do. Although it’s never possible to achieve absolute certainty when detecting such attacks, Apple has high confidence in this warning — please take it seriously.
“We are unable to provide more information about what caused us to send you this notification, as that may help mercenary spyware attackers adapt their behavior to evade detection in the future.
“Mercenary spyware attacks, such as those using Pegasus from the NSO Group, are exceptionally rare and vastly more sophisticated than regular cybercriminal activity or consumer malware.”
According to Apple, the notification also included steps that users can take to protect their device, including enabling Lockdown Mode, where certain apps, websites and features are restricted to reduce the attack surface for spyware.
A mercenary spyware attack occurs when spyware — malicious software used for surveillance purposes — is deployed onto a target device by a third-party entity. This entity does so on behalf of a paying client and aims to gather the required sensitive information or conduct surveillance without the direct involvement of their sponsor.
Spyware typically infiltrates a device through vulnerabilities in software or through deceptive acts like phishing. Once installed, it can monitor communications like emails, texts and phone calls, track locations, steal passwords, access files and even remotely control the device. Any data collected can be covertly sent to the operator.
SEE: New GoFetch Vulnerability in Apple’s M Chips Allows Secret Keys Leak on Compromised Computers
The spyware will function without alerting the user and can be deployed on any device that connects to the internet. It is extremely difficult to know whether a device has been infected without detailed forensic analysis.
According to the Apple support page, individually targeted attacks of this nature “have historically been associated with state actors, including private companies developing mercenary spyware on their behalf, such as Pegasus from the NSO Group.”
Apple added that mercenary spyware attacks are “vastly more complex” than typical malware attacks and “cost millions of dollars” to deploy due to an exceptional amount of resources being used against a small group.
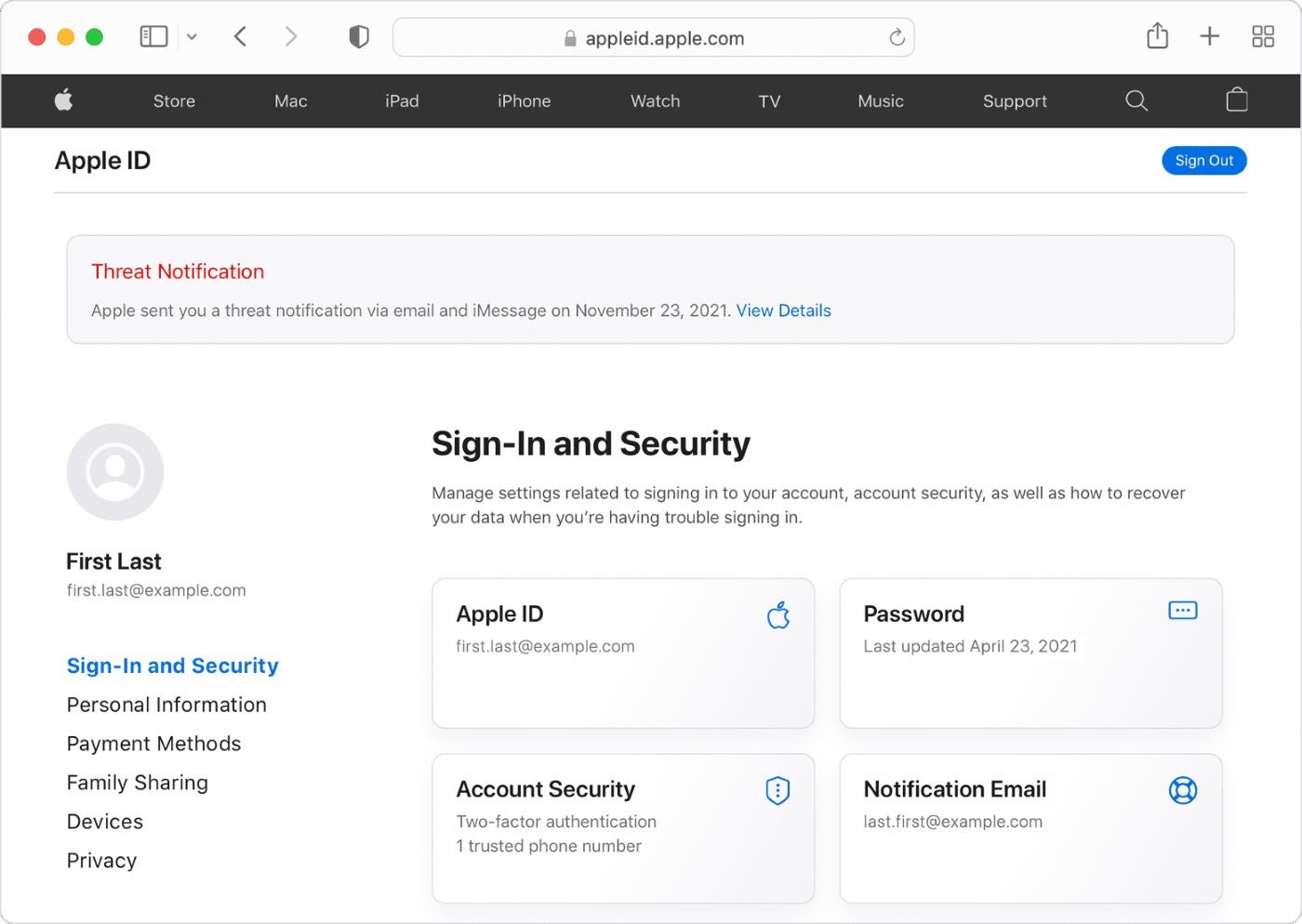
Apple said its threat notifications (Figure A) are “designed to inform and assist users who may have been individually targeted by mercenary spyware attacks.” The notifications do not necessarily mean that spyware has been successfully implanted in the user’s device.
Figure A
If a user is suspected of being targeted, they will receive a notification on any device where they are signed in with their Apple ID. A message is sent both via email and iMessage, and a notification appears at the top of the webpage appleid.apple.com.
The tech giant said it uses “internal threat-intelligence information and investigations” to detect mercenary spyware attacks, but cannot reveal exactly what triggers a threat notification “as that may help mercenary spyware attackers adapt their behavior to evade detection in the future.”
Apple added that the threat notifications are “high-confidence alerts” that a device has been targeted in a spyware attack, but its investigations “can never achieve absolute certainty.”
According to Amnesty International, forensic tests conducted by them and other civil society groups on devices that have received such notifications and reported: “In many cases these forensic checks have confirmed that the devices of people who had received the notifications were indeed targeted and compromised with advance spyware.”
According to Apple, the company has been sending threat alerts like this since 2021 and does so multiple times a year. To date, users in 150 countries have been notified of a similar attack.
The last time Apple sent out a threat notification was on October 31, 2023, and it was received in multiple countries. The recipients were notified that they were being targeted by “state-sponsored attackers”; since then, Apple no longer uses the state-sponsored term in its threat notification policy, as reported by Reuters. In December 2023, Amnesty International revealed that the Israeli surveillance firm NSO Group was behind the October attack after deploying the spyware Pegasus on journalists.
Research has found that 97% of all executives now access work accounts through their personal devices, with the figure increasing to 99% for the C-suite. This creates a backdoor for cybercriminals to access sensitive corporate data through spyware, so employees must take steps to ensure their device is secure.
SEE: Mobile device security policy (TechRepublic Premium)
Apple offers the following advice to all users to help protect themselves against all types of malware: